Features
System operators easily and securely change encryption keys on a regular basis.
If a radio is compromised you have the ability to:
• Remote inhibit – Securely prevent radios from gaining access to the network from a distance
• Remote enable – Securely re-establish a radio’s network access from a distance
• Zeroize – Securely remove a radio’s key material
• Change-over – Securely switch a radio’s keyset to another keyset for use
Specification Sheet
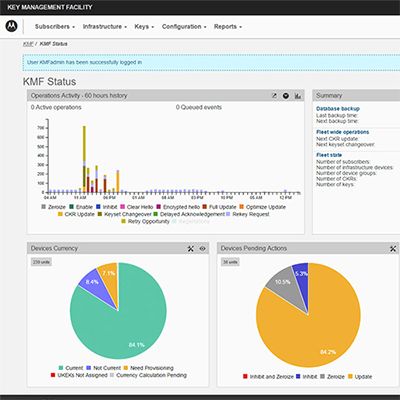
Key Management Facility
Key Management Facility